Proxies can bring many benefits to their users: they can influence the speed of traffic flow, its security, and accessibility. They can also be great helpers when extracting data from websites, preventing your IP address from getting blocked or blacklisted while scraping.
Need an introduction to proxies? Find out how a proxy server works and why people use them.
But for the proxy to work in accordance with the user’s needs, it has to be configured and selected accordingly. This article will look at the various types of proxies based on how they obtain their IP addresses, their direction of traffic flow, service, and level of anonymity.
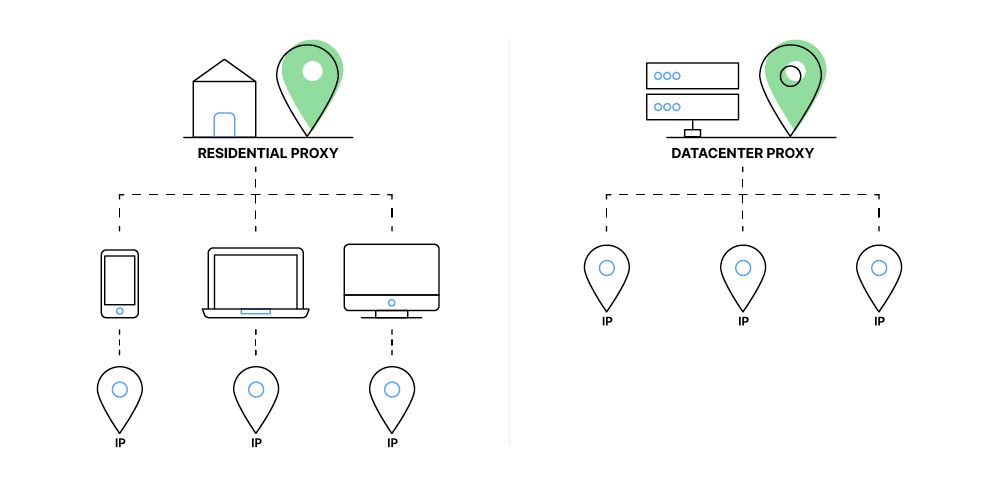
Proxies based on location of IP address
A proxy’s primary goal is to hide your IP address by replacing it with a new one. There are two main proxy types based on how they acquire this IP and where it is located:
Residential proxies
These proxies use IP addresses provided directly by ISPs (Internet Service Providers) and are therefore linked to actual homes and devices in various cities and countries. This makes the proxy almost indistinguishable from a regular user, making it much harder for websites to identify a proxy user and block them. Residential proxies are often used for IP address rotation, which can be very helpful when web scraping and choosing a bot detection tool. But since these IPs need to be bought or rented from ISPs, they are naturally more expensive to operate.
There are also other specialized types of residential proxies - static and mobile proxies, which are generally more expensive. While static proxies are connected to a single IP home address, mobile proxies use devices connected to a mobile network connection (e.g., 3G, 4G, or 5G). Although both can be used to change geographical location, mobile proxies appear more genuine, making them harder for anti-bot systems to identify. On the other hand, static proxies can be used in situations where a user needs the same IP address for recurring sessions. This can be useful when dealing with social media and other networks that require the user to log in.
Datacenter proxies
Datacenter proxies are not provided by ISPs, but rather from third parties such as web hosting services and are hosted in data centers worldwide. While they are cheaper and faster, they are easier to get blacklisted if the user is doing traffic-intensive tasks, since, compared to residential proxies, the IP does not belong to an actual home.
Related: Datacenter proxies: when to use them and how to make the most of them
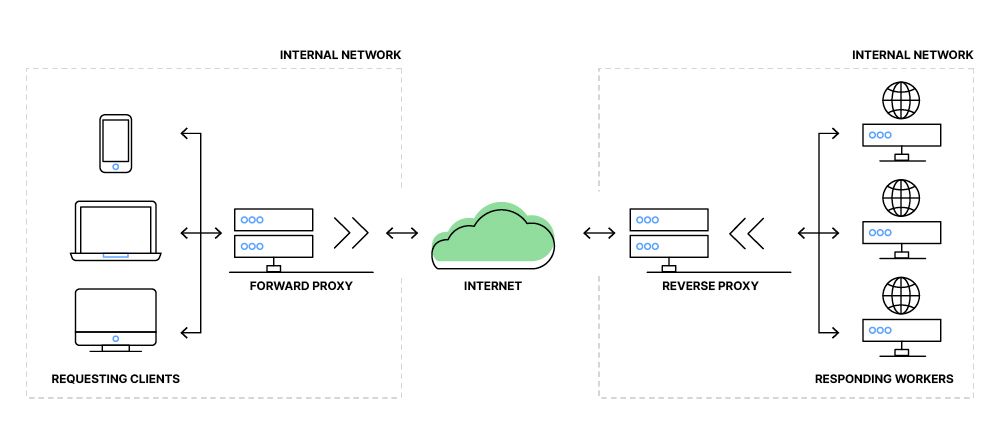
Proxies based on direction of traffic flow
Just like any other traffic, proxies can also be inbound or outbound based on if they’re set up on the client or the server-side:
Forward proxies
Forward proxies are a general type of proxy, where a client sets up an alternative IP address to gain access to blocked websites or simply to hide and mask their identity. This can also be set up on an entire network of users, granting or denying their requests for websites and caching them for faster access.
Because all requests pass through the proxy server, internet speed may vary depending on server load, distance, and bandwidth. Running an internet speed test with and without the proxy helps identify any slowdown.
Reverse proxy
While forward proxies protect clients, reverse proxies do the same for servers. So whenever a client makes a request, it does not go directly to the server but to the proxy, which acts on its behalf. Although these proxies are great for security and caching, another benefit is load balancing. So if a proxy takes care of multiple servers with the same purpose, it tries to direct the traffic evenly, preventing lag or delays.
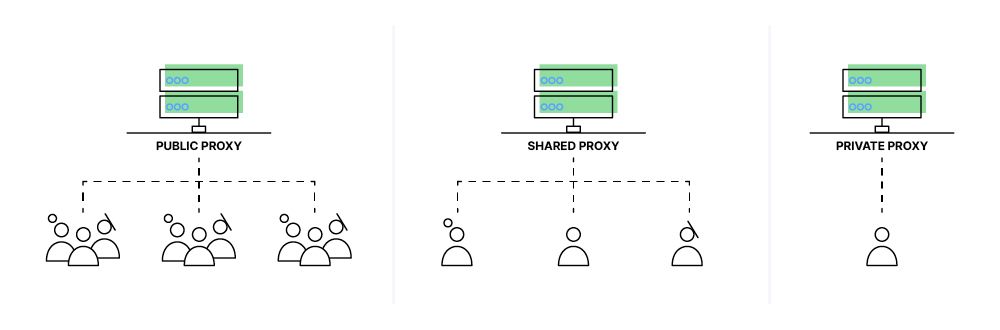
Proxies based on service
Often, unique IP addresses provided by proxies are not used solely by one user but by many. This can impact the internet speed and security - one user gets blocked by a website = all users get blocked. Therefore, we can divide proxies based on the number of people that share an IP.
Related: Get proxies: 10 free or low-cost proxy services
Public proxy
These proxies can generally be found online in various proxy lists and are used by anyone with a functional internet connection. They are usually free, but since their moderators are often anonymous, security can be an issue, not knowing who has access to the user’s browsing data. Because so many people use them simultaneously, they can be pretty unstable and blocked by websites. This traffic overload can also affect broadband speed.
Shared proxy
Unlike public proxies, these come at a cost but are still on the cheaper side. They are shared by a group of people who pay for a certain proxy service, which has a set of features like customer support in case something goes wrong. They are also more reliable and secure since the user and the company have to agree to terms of service. But a shared proxy can also have speed issues if more of its users are doing traffic-intensive tasks.
Private proxy
These proxies are typically hosted on a Virtual Private Server (VPS), ensuring stable performance and reliability. A private, or a dedicated proxy, is a proxy used solely by one specific user. This way, there is no lag, delay, or traffic overload. This is the most expensive type, which can be over five times the price of a shared proxy server. Also, using the same IP for an extended period of time can have some drawbacks in terms of anonymity.
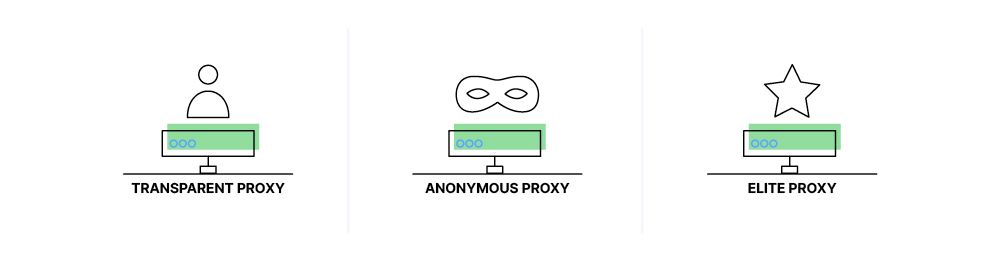
Proxies based on level of anonymity
Sometimes, a proxy forwards information about its client through “headers,” which are sent along with the requested data. These headers are often used inside companies or closed networks to monitor the users’ traffic. Based on what header information the proxy server forwards, we can differentiate several proxy types:
Transparent proxy
Transparent proxies are the least anonymous since they forward the user’s actual IP address in the X-Forwarded-For header and the proxy used in the Via header. Since these proxies are not meant to protect an individual user’s privacy, they are mainly used to restrict content or cache frequently visited websites, resulting in faster load times.
Anonymous proxy
While anonymous proxies do not include your real IP in the X-Forwarded-For header, they still give out the information that you’re using a proxy in the Via header. Despite this, they remain the most popular forwarding proxy type, are great for general web use and, when combined with IP rotation, are very difficult to reliably identify.
Elite proxy
This proxy’s priority is to protect the user by providing fake or no information regarding the user’s real IP and the proxy status. This way, the user appears to be authentic, without a trace of proxy use.
With so many proxy types to choose from, it is essential to look at the pros and cons of the variety and try to find an optimal solution. Apify Proxy, for instance, is an elite proxy using a combination of datacenter and residential IP addresses to find the perfect balance between performance and price for web scraping purposes.
Related: The 7 best proxy providers for web scraping in 2024
Every new Apify account comes with a free trial of Apify Proxy, so sign up now and try it out with one of the hundreds of web scraping tools on Apify Store.
A series of our answers to FAQs on using proxies for web scraping